Why a Process-Driven IT Approach Saves Businesses More Money Than Reactive IT Support
Why a Process-Driven IT Approach Saves Businesses More Money Than Reactive IT Support
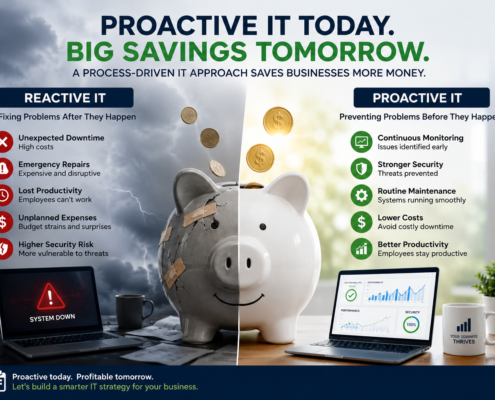
Many businesses view IT support as something they only need when a problem occurs. A server crashes, an employee can’t access email, or a cyberattack disrupts operations—and then the IT team is called to fix it. While this reactive model may seem cost-effective on the surface, it often leads to significantly higher costs over time.
A Process-Driven IT Approach focuses on preventing issues before they impact business operations. Through proactive monitoring, routine maintenance, security management, and documented procedures, businesses can avoid costly downtime and maximize the value of their technology investments.
What Is a Process-Driven IT Approach?
A Process-Driven IT Approach is a structured method of managing technology through documented procedures, preventative maintenance, and continuous monitoring. Rather than waiting for systems to fail, IT professionals follow established processes designed to identify and resolve issues before they become business disruptions.
Common proactive IT processes include:
- System monitoring
- Patch management
- Cybersecurity assessments
- Backup verification
- Disaster recovery planning
- User onboarding and offboarding
- Network performance monitoring
- Hardware lifecycle management
These processes work together to create a stable, secure, and reliable technology environment.
The Hidden Cost of Reactive IT
Many organizations underestimate the true cost of downtime.
When critical systems fail, businesses often experience:
- Lost employee productivity
- Missed sales opportunities
- Delayed customer service
- Overtime expenses
- Emergency repair costs
- Damage to customer trust
According to research from the IT industry, downtime can cost organizations thousands of dollars per hour depending on business size and operational complexity. Source: https://www.ibm.com/topics/downtime
The financial impact extends far beyond the immediate repair bill.
Preventing Problems Costs Less Than Fixing Them
One of the greatest advantages of a Process-Driven IT Approach is prevention.
For example, a proactive patch management process helps identify and install security updates before vulnerabilities can be exploited. A routine hardware review may reveal aging equipment before it fails unexpectedly. Regular backup testing ensures data can be recovered when needed.
These preventative activities often require only a fraction of the cost associated with recovering from a major outage, ransomware attack, or hardware failure.
Think of it like maintaining a vehicle. Regular oil changes and inspections are far less expensive than replacing an engine that failed due to neglect.
Improved Cybersecurity Reduces Financial Risk
Cybersecurity incidents have become one of the largest financial threats facing small and mid-sized businesses.
A proactive IT strategy includes processes such as:
- Vulnerability scanning
- Security awareness training
- Multi-factor authentication implementation
- Endpoint protection management
- Access control reviews
- Incident response planning
According to the Cybersecurity and Infrastructure Security Agency (CISA), organizations that implement security best practices significantly reduce their exposure to common cyber threats. Source: https://www.cisa.gov
By identifying risks early, businesses can avoid the substantial costs associated with data breaches, ransomware recovery, regulatory fines, and reputational damage.
Increased Productivity Through Reliable Systems
Employees are most productive when technology simply works.
When businesses operate under a reactive IT model, recurring technical issues often go unresolved until they become major problems. This creates frustration, delays projects, and reduces overall efficiency.
A Process-Driven IT Approach focuses on maintaining system health continuously. Regular monitoring helps identify performance issues before users notice them, while documented support processes ensure faster issue resolution when problems occur.
The result is less downtime and more productive employees.
Better Budgeting and Predictable IT Costs
Emergency IT repairs can be expensive and difficult to budget for. Reactive support often creates unpredictable expenses that strain business finances.
By contrast, proactive IT management helps organizations forecast technology investments more accurately. Planned hardware replacements, scheduled upgrades, and ongoing maintenance reduce the likelihood of unexpected expenditures.
Businesses gain greater control over both their technology environment and their IT budget.
Supporting Long-Term Business Growth
As businesses grow, technology environments become more complex. A reactive approach that may work for a small organization often becomes unsustainable as user counts, devices, and applications increase.
Documented processes create consistency and scalability. They allow businesses to onboard employees efficiently, maintain security standards, and support growth without sacrificing reliability.
Organizations that adopt proactive IT management are better positioned to adapt to changing business needs while minimizing operational disruptions.
Conclusion
The question is no longer whether businesses can afford proactive IT management—it is whether they can afford not to have it.
A Process-Driven IT Approach helps organizations reduce downtime, strengthen cybersecurity, improve productivity, and avoid costly emergency repairs. By investing in preventative processes instead of constantly reacting to problems, businesses create a more stable and cost-effective technology environment.
The most successful organizations understand that IT is not just about fixing problems. It is about implementing processes that prevent problems from occurring in the first place.
To request a free consultation or for additional information, visit: https://nomadtechgroup.com



 How MSPs Save Small Business Owners Money
How MSPs Save Small Business Owners Money



